The Problem
Authorization Was Built for Simpler Times
It worked when users logged in and accessed monoliths. But today's architectures involve APIs, microservices, event streams, and AI agents, and authorization hasn't kept up.
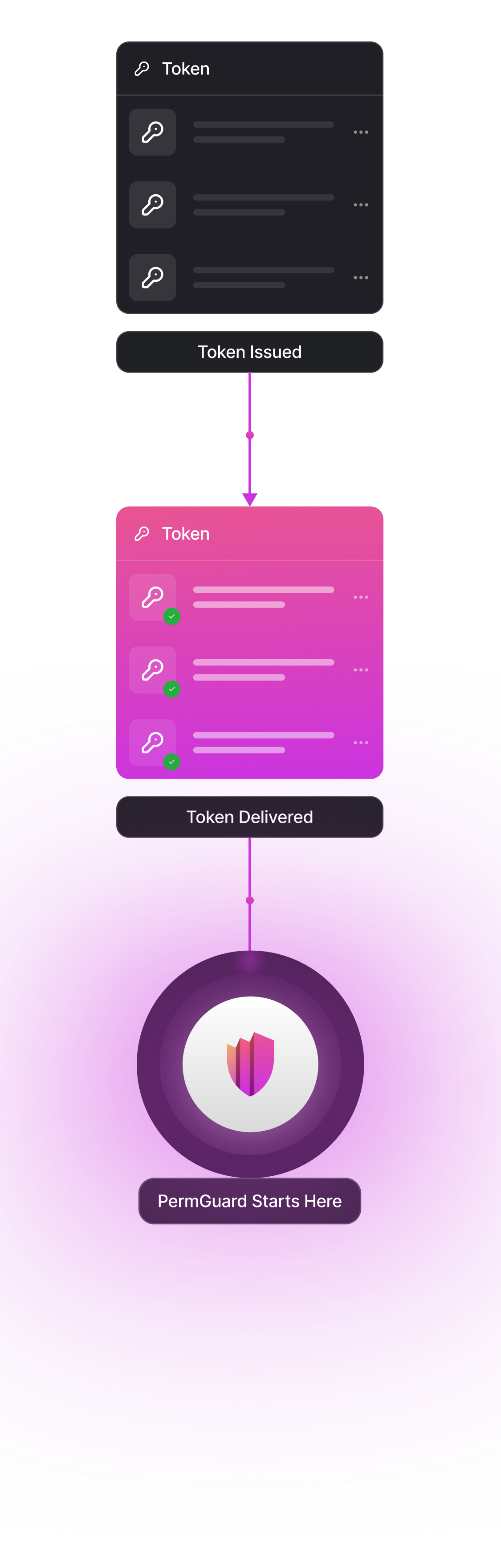
Beyond The Tokens
Where Tokens Stop, Risk Begins
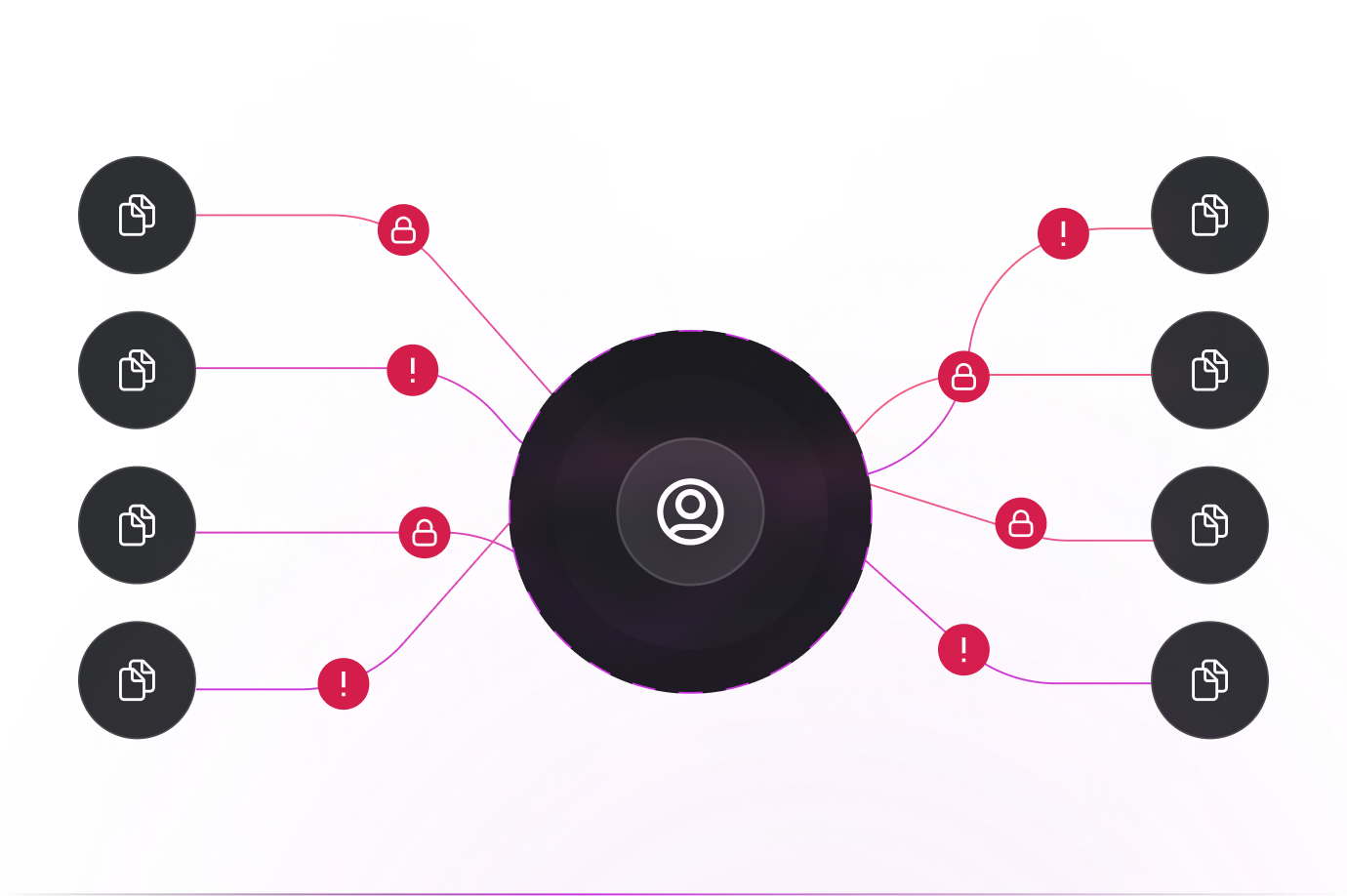
While tokens carry identity and scopes, they don't guarantee how, or even if, those scopes are enforced. Scopes offer a simplified view of authorization, but rarely capture its full complexity.
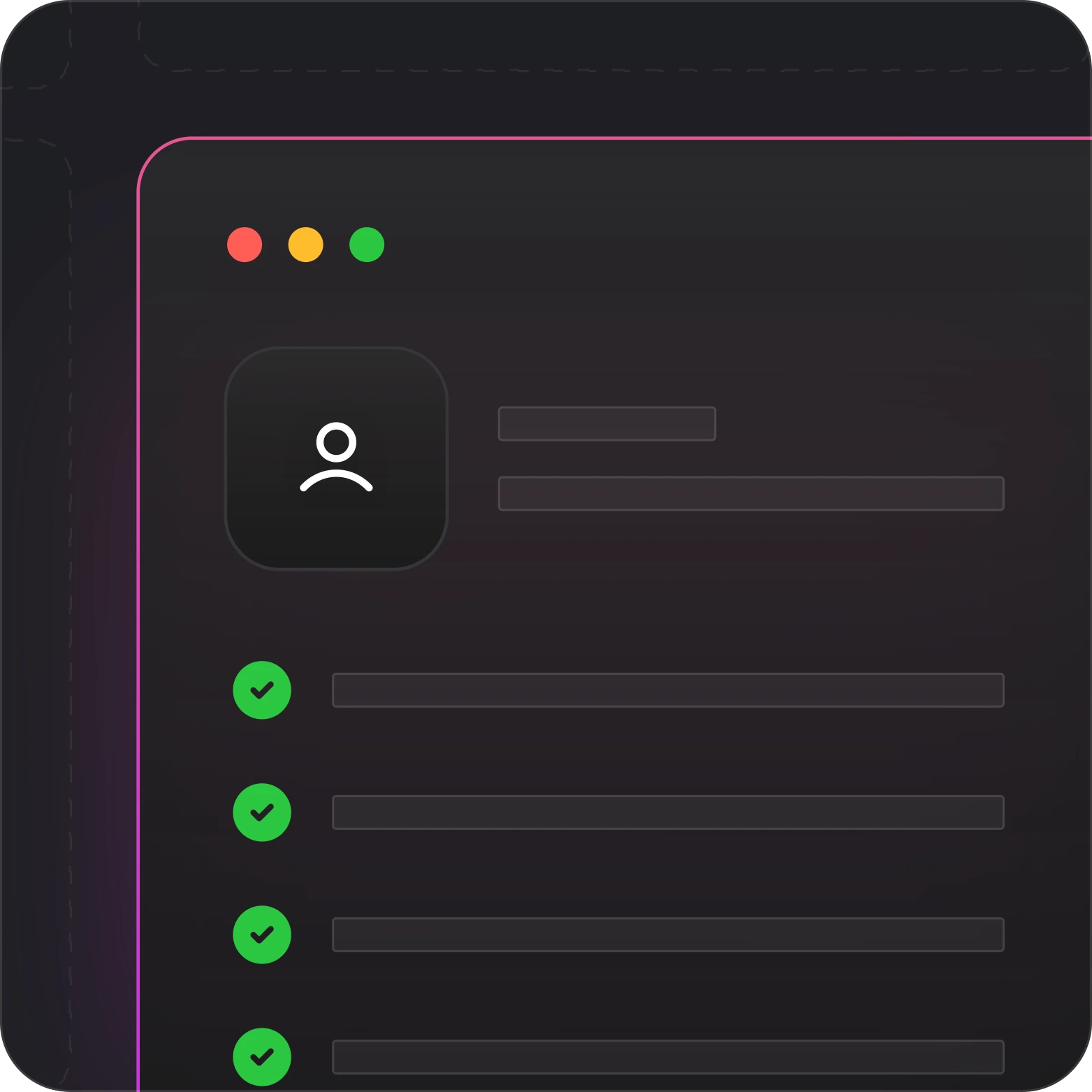
Beyond The Tokens
What Traditional Authorization Gets Wrong

No standard for validation

No guarantee of consent or scope enforcement

No visibility or audit trail

Silent delegation risks

Tied to identity provider

Authorization Must Work for Machines, Agents, and APIs
Most systems were designed for human access. But in modern environments, services and ai agents make decisions, often on someone else's behalf.
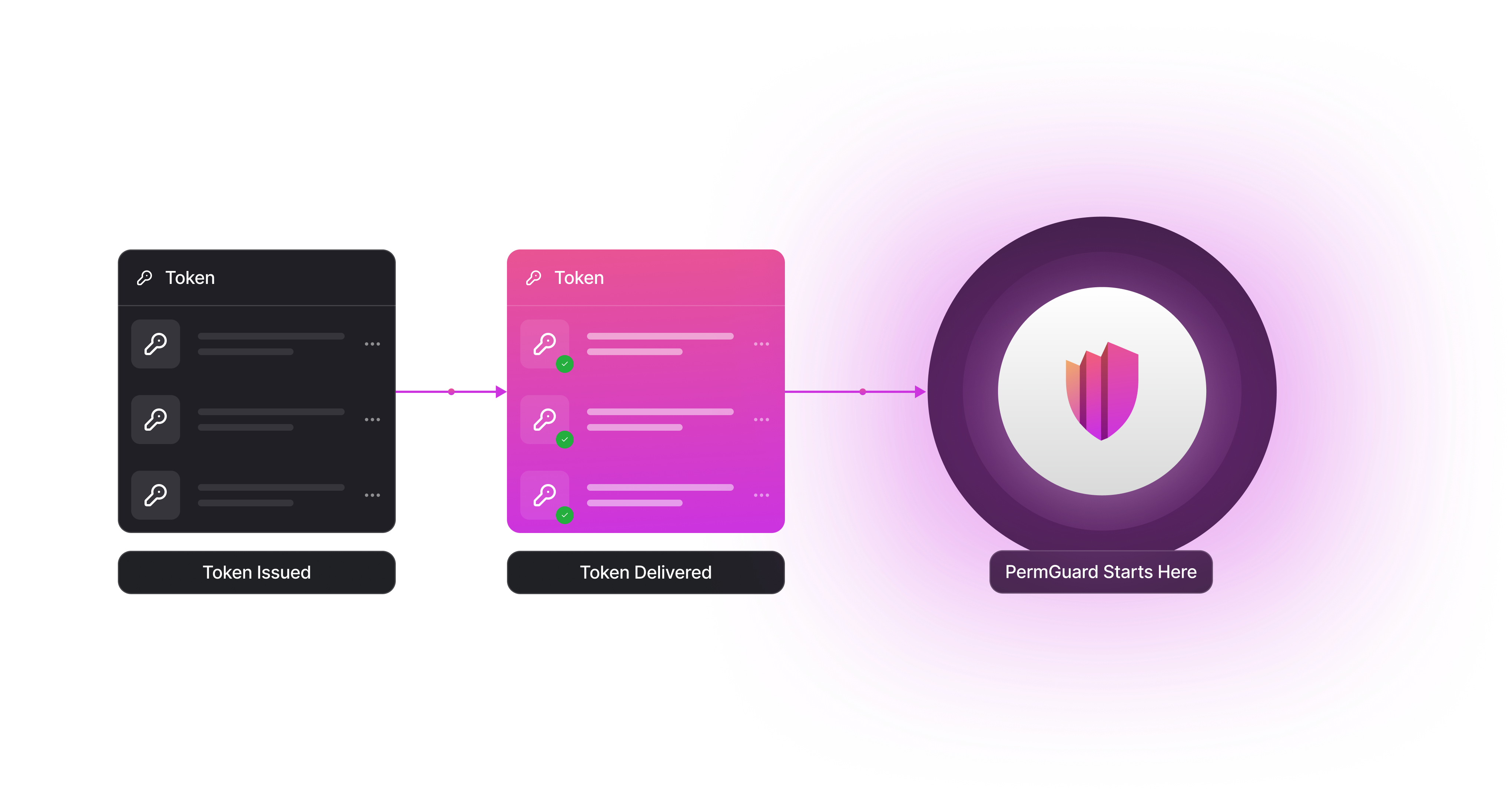
Trust Must Be Defined, Verified, and Audited
Current systems assume workloads are safe, scopes are enforced, and actions are legitimate, without any proof. Permguard turns assumptions into verifiable enforcement.

The Trust Layer Between Identity and Action
Permguard is the missing layer that governs who can act, on whose behalf, and under what conditions, with full visibility and auditability.
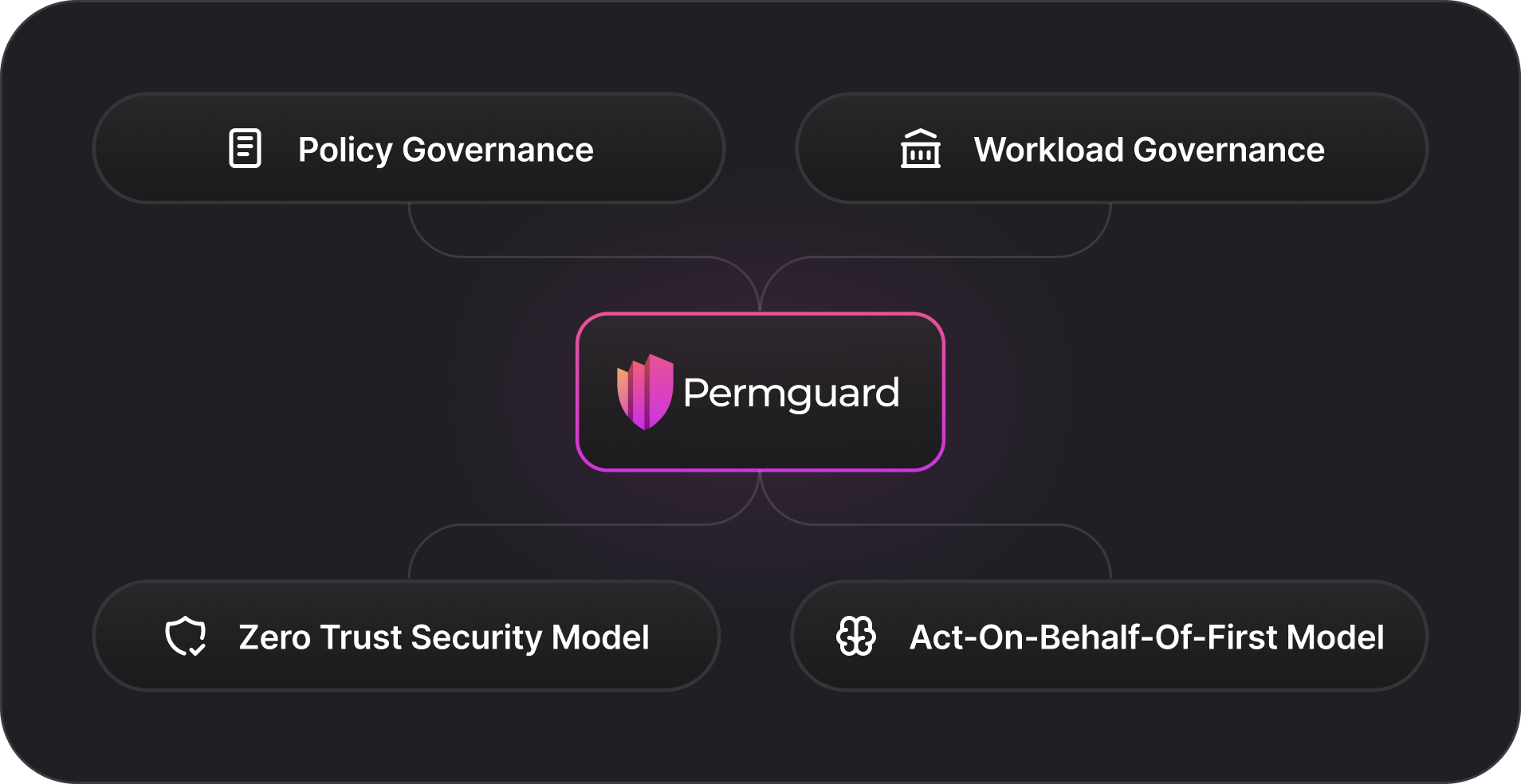
Core Principles of Permguard

Policy Governance
Immutability, versioning, and externalized control

Workload Governance
Defines who can act, not just who you are

Zero Trust Security Model
Dual validation of both subject and workload

Act-On-Behalf-Of-First Model
On-behalf-of execution with verifiable consent
Authorization is Evolving. Permguard Leads the Way.

From portable tokens to portable trust.

From implicit assumptions to policy-based control.

From local checks to global governance.